.png)
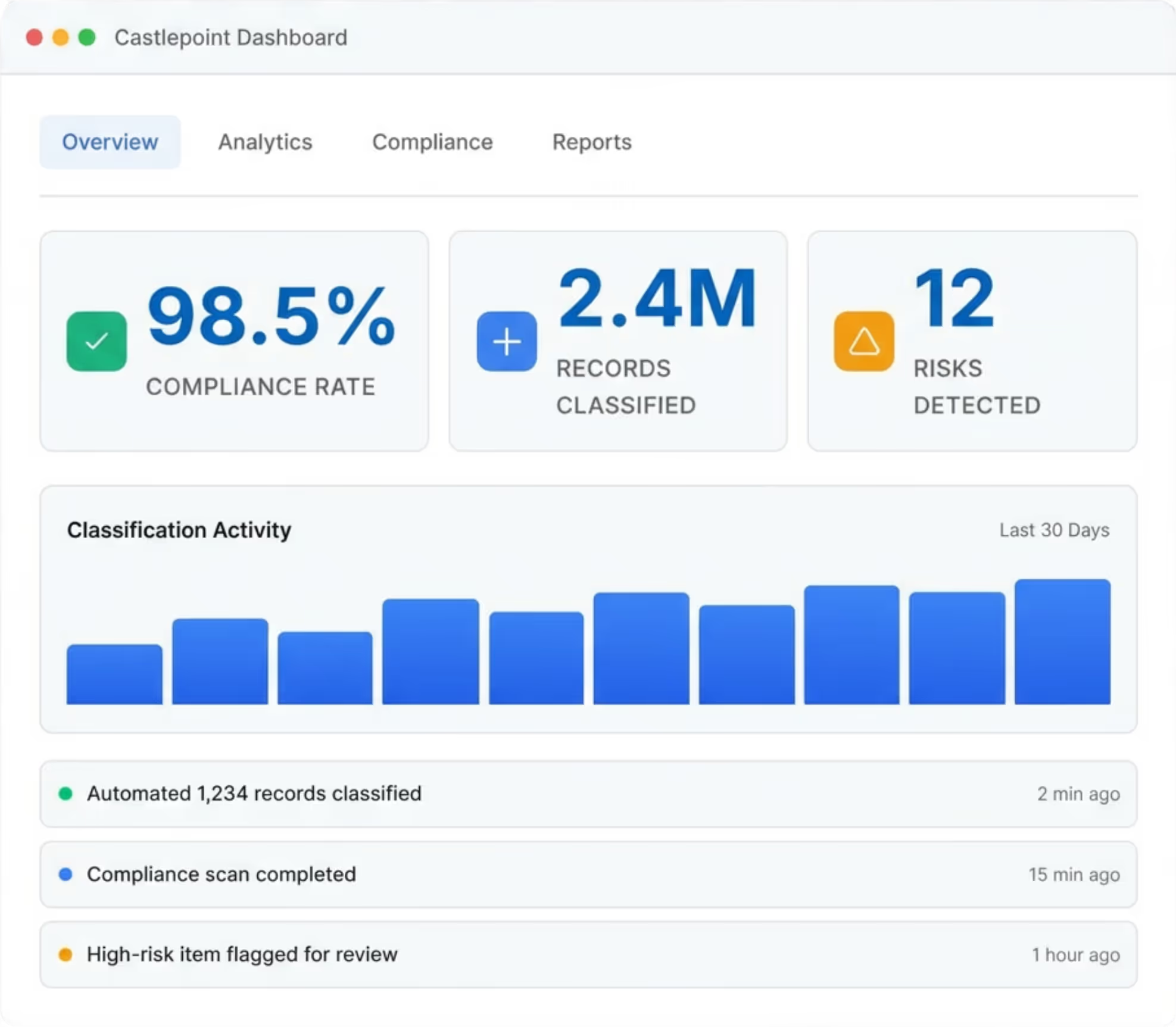
Privacy management
Ensure compliance with privacy regulations by understanding and applying the relevant laws to various data sets, and meeting your data minimisation needs.
Automatically discover and classify data across all systems with Explainable AI. Reduce risk, meet regulatory obligations and enable safe GenAI, without disrupting your environment.
True auto-classification. Explainable AI.
“With Castlepoint’s AI capabilities, we can know what data we have, where it is and who is doing what to it to determine the inherent risk and value and what rules apply to it. And we can do this with no impact on users, source systems or source data.”
The Commonwealth Treasury
Castlepoint’s ethical AI automates records classification, helping organisations preserve or lawfully destroy records, significantly reducing the risk of data breaches and financial or reputational damage.
Disable the labels. Autoclassification based on content: no metadata, tags, or labels required.


“Castlepoint has helped us ensure we understand the sensitive information we store, and we now have granular visibility into what data we hold, where it lives, and when it must be destroyed."

“We are now in a better position to be able to protect our people and intellectual property from harm or loss…and reduce workload across the team. The Castlepoint team has been great to work with from first engagement. You can always reach a real person to talk with, and jobs logged through their ticketing system have quick turnaround times.

[Castlepoint] provided staff with a seamless record keeping approach with minimal input by users to create and file records. The new EDRMS is also guided by government privacy policies and provisions for secure storage of information”



























































